Security of the cloud aws is responsible for protecting the infrastructure that runs aws services in the aws cloud.
Aws ec2 container service security.
Security in amazon elastic container service cloud security at aws is the highest priority.
The containers are launched on ec2 instances that you own and control.
Aws also provides you with services that you can use securely.
Customers such as duolingo samsung ge and cookpad use ecs to run their most sensitive and mission critical applications because of its security reliability and scalability.
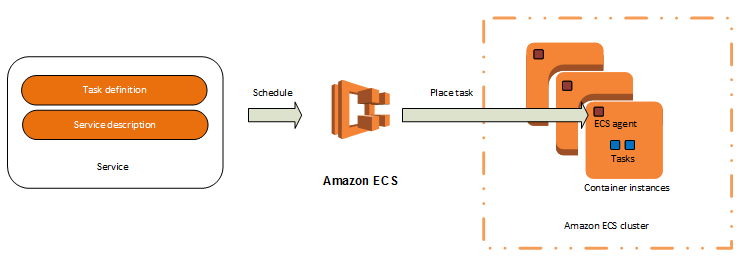
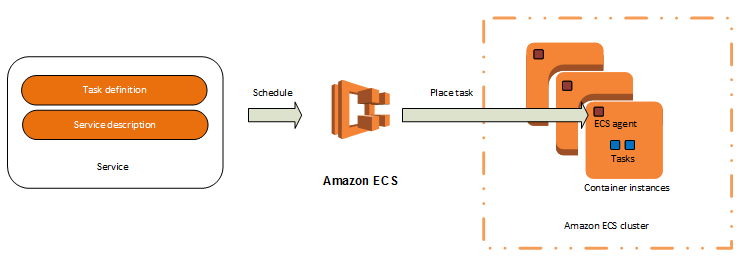
The aws ec2 container service is a cluster management system that streamlines the use of docker images on a set of aws instances.
As an aws customer you benefit from a data center and network architecture that is built to meet the requirements of the most security sensitive organizations.
Third party auditors regularly test and verify the effectiveness of our security as part of the aws compliance programs.
Note your aws account number because you ll need it for the next task.
Amazon elastic container service amazon ecs is a fully managed container orchestration service.
Using ec2 container service ecs was designed to be easy to set up and.
Services in aws such as amazon ec2 and amazon ecs require that you provide credentials when you access them so that the service can determine whether you have permission to access its resources.
Since your applications will run on ec2 instances you will have access to all the security controls generally available to those resources.
The tasks can take advantage of iam roles security groups and other aws security features.